Integrated Fleet Key Management Solutions for Fleets
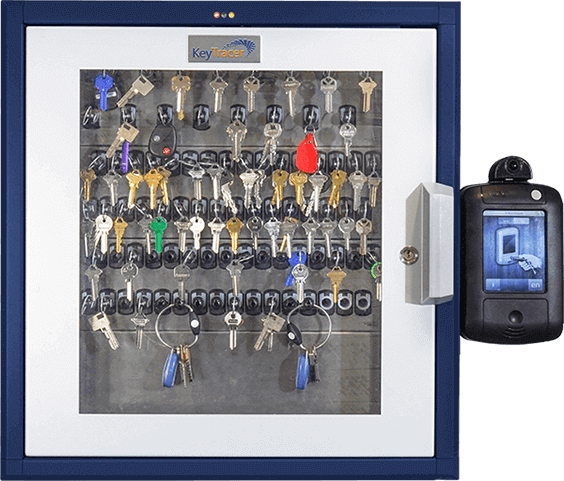
Track and manage your vehicle keys using a secure and automated fleet key control system.
- Allow drivers to schedule vehicle use.
- Remotely manage maintenance and inspection schedules.
- Get real-time insights on damage and driver performance issues.